Cybercriminals don’t break in anymore — they log in. And in 2026, phishing has evolved into something far more convincing, faster‑moving, and AI‑powered than anything we saw even a year ago.
As your MSP, our job at WilTech Support is to keep you informed, protected, and confident. This guide breaks down the newest phishing tactics we’re seeing in the wild and what we’re doing to keep your business safe.
🎣 What Phishing Looks Like in 2026
Phishing is still the same core idea: someone pretends to be a trusted person or company to trick you into giving up something valuable — usually your Microsoft 365 credentials, financial info, or access to your systems.
But the methods have changed dramatically.
1. AI‑Generated Emails That Look Perfect
Gone are the days of bad grammar and weird logos. Attackers now use AI to:
- Clone writing styles
- Copy real email threads
- Generate flawless invoices
- Mimic internal communication tone
These emails often look identical to the real thing. Even trained eyes can struggle.
2. Deepfake Voice & Video Phishing
This is the fastest‑growing threat of 2026.
Attackers can now generate:
- A phone call that sounds exactly like your boss
- A video call where the “person” on screen looks and moves like your co-worker
- A voicemail requesting an urgent wire transfer
This isn’t science fiction — it’s already happening to businesses worldwide .
3. Compromised Contacts (The Most Common Attack We See Locally)
This is the one hitting small businesses the hardest.
Here’s how it works:
- A vendor, customer, or partner gets hacked.
- The attacker downloads their email history.
- They create a look‑alike email address pretending to be you.
- They message people you’ve emailed before, asking for payments, documents, or login info.
You never see the attack. You never get the email. But your reputation takes the hit.
4. Homoglyph & Typosquatting Domains
Attackers register domains that look nearly identical to yours:
- wiltechservlces.com (L instead of i)
- wiltechservice.co
- wiltech‑support.com
These domains are used to send fake invoices, contracts, or DocuSign links that appear legitimate at first glance .
5. “Smishing” and “App‑Based” Phishing
Phishing is no longer just email.
We now see attacks through:
- Text messages
- Facebook Messenger
- Instagram DMs
- LinkedIn messages
These often impersonate Microsoft, banks, or shipping companies.
🧠 How to Spot a Phishing Attempt in 2026
Even with AI‑polished messages, the behavior of phishing hasn’t changed.
Look for:
- Urgency (“Your account will be closed in 1 hour”)
- Requests for credentials
- Unexpected attachments or DocuSign links
- Payment changes (“Use this new bank account”)
- Emails from vendors that don’t match their usual tone
- Phone calls asking you to “verify” anything
If something feels off, it probably is.
🛡️ How WilTech Protects You
Phishing is a people problem and a technology problem. So we defend you on both fronts.
1. Microsoft 365 Hardening
We enforce:
- MFA everywhere
- Impossible‑travel detection
- Login risk scoring
- Geo‑blocking (if applicable)
- Suspicious inbox rule monitoring
- OAuth app consent restrictions
These stop most credential‑theft attempts before they start.
2. Advanced Email Filtering
We use modern filtering that blocks:
- Malicious links
- Spoofed domains
- Look‑alike senders
- Sandboxed attachments
- Real‑time link scanning
This dramatically reduces what reaches your inbox.
3. Domain Protection
We implement:
- SPF
- DKIM
- DMARC enforcement
- Look‑alike domain monitoring
This helps prevent attackers from impersonating your business.
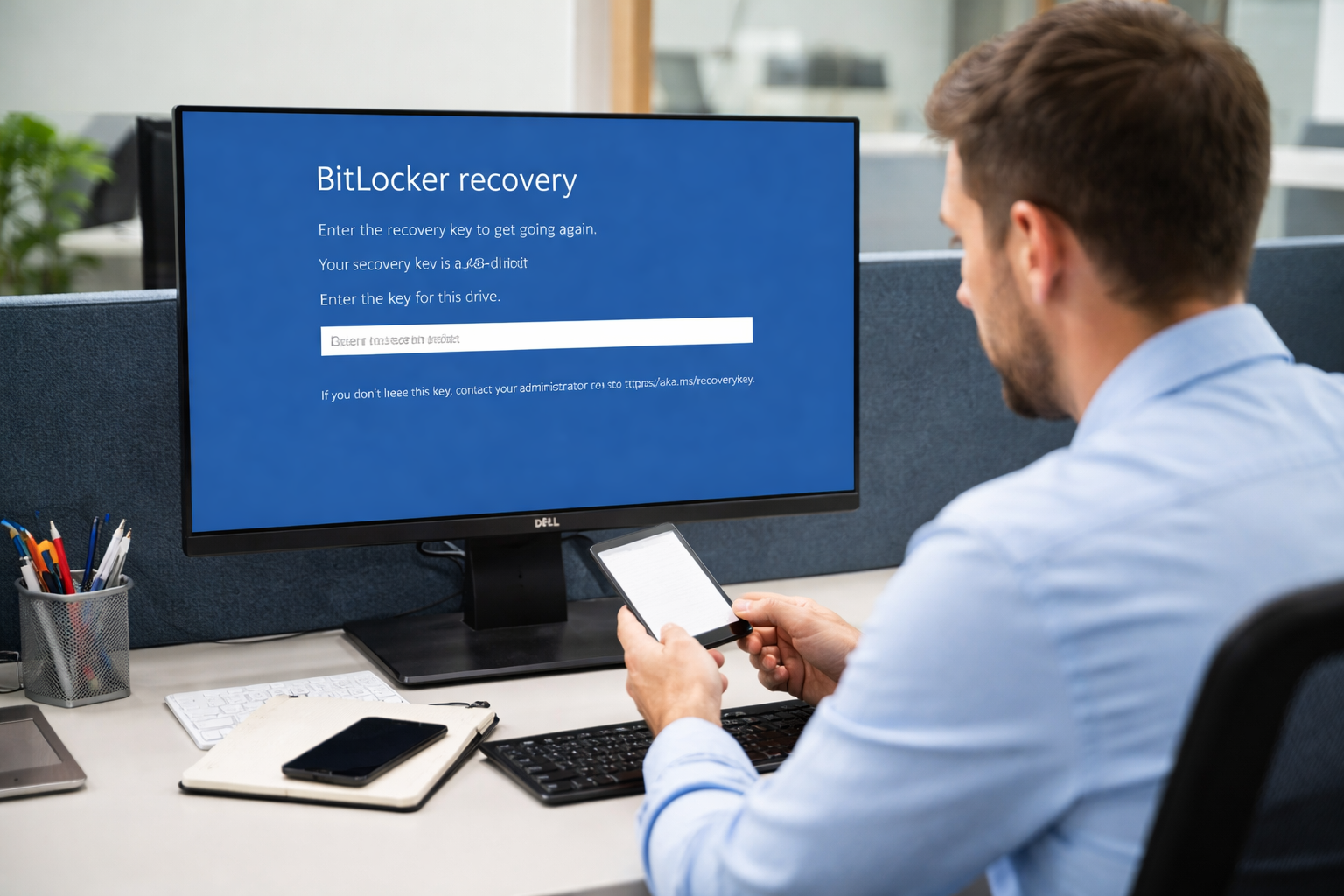
4. Rapid Incident Response
If a phishing email slips through or someone clicks:
- We revoke sessions
- Reset credentials
- Remove malicious inbox rules
- Quarantine the email across all mailboxes
- Investigate the source
- Notify affected contacts if needed
Speed matters — and we move fast.
5. Employee Awareness Training
Short, practical, real‑world training that teaches your team:
- How to spot modern phishing
- What to do when something feels off
- How to report suspicious messages without fear
No boring annual videos. Just useful habits.
🏡 What You Can Do as a Business Owner
Here’s the simple version:
- Never approve payment changes without a phone call
- Never trust a link you didn’t expect
- Never give credentials over email or phone
- Always verify unusual requests through a second channel
- Call us immediately if something feels wrong
You don’t need to be a cybersecurity expert — that’s our job.
✔️ Final Thoughts
Phishing isn’t going away. It’s getting smarter, faster, and more personal.
But with the right protections — and a partner who stays ahead of the curve — your business can stay safe, confident, and resilient.
If you’d like us to review your current protections or run a phishing‑resilience check for your team, we’re here to help.