Introduction to Home Network Security
In today’s digital age, securing a home network has become an essential aspect of safeguarding personal information and maintaining privacy. With the increasing reliance on internet-connected devices, the home network is often the backbone for many online activities, from banking and shopping to accessing sensitive information. However, this dependency also makes home networks attractive targets for cybercriminals. Understanding the importance of network security is vital for anyone looking to protect their digital lives.
Many common vulnerabilities can threaten the integrity of a home network. Outdated routers, weak passwords, and devices lacking security updates can provide easy entry points for unauthorized users. In addition, consumers often overlook the importance of securing Internet of Things (IoT) devices, which can be particularly susceptible to attacks. These devices, ranging from smart thermostats to security cameras, can be exploited if not appropriately managed, thereby compromising network security.
The potential consequences of not securing a home network can be severe. Data breaches can lead to identity theft, financial loss, and unauthorized access to personal and sensitive data. Moreover, the ripple effects of a compromised network can extend to other connected devices, turning a home network into a conduit for larger-scale attacks on other systems. Given these risks, it is essential for homeowners to take proactive measures in fortifying their network against threats.
Awareness of these challenges can motivate individuals to implement effective security practices. Whether through installing a reliable firewall, utilizing a secure DNS, or ensuring device isolation, understanding the significance of home network security is paramount. By prioritizing these protective measures, homeowners can enhance their digital safety and create a more secure online environment for themselves and their families.
Understanding the Basics: What is a Router and Why Secure It?
A router plays a crucial role in a home network by serving as the primary device that connects various devices to the internet. It manages both local and internet traffic, facilitating communication between devices such as computers, smartphones, tablets, and IoT devices. The fundamental function of a router involves receiving data from the internet and distributing it to the connected devices on the network while also ensuring that data from these devices reaches its proper destination online. This strategic management of data packets is essential for maintaining uninterrupted internet connectivity.
Given its integral role, securing a router is paramount in safeguarding a home network. When a router is not adequately secured, it becomes vulnerable to a myriad of cyber threats, including unauthorized access and cyberattacks. These threats can lead to data breaches, identity theft, or even the takeover of connected devices. As a result, a router should be viewed as the first line of defense against such risks. To achieve this, users must implement several security measures, including changing default credentials, enabling network encryption, and updating firmware regularly.
Furthermore, a router acts as a gatekeeper for all incoming and outgoing internet traffic. By configuring security settings, users can control which devices can connect to their network, thereby limiting exposure to potential threats. For instance, ensuring that guests do not access the main network can help protect personal devices from malicious attacks. Additionally, employing features such as firewalls and device isolation can further augment the security of the router. Ultimately, understanding the importance of securing a router is essential in establishing a robust home network that can effectively resist cyber vulnerabilities.
Router Hardening: Steps to Secure Your Device
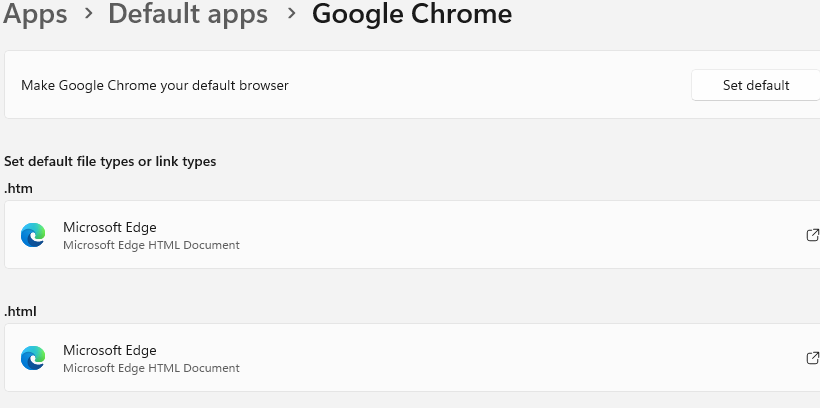
Securing your home network begins with the router, as it serves as the gateway to the internet and can be a potential target for intrusions. One of the first and most critical steps in router hardening is to change the default login credentials. Routers typically come with preset usernames and passwords, which are widely known and easily accessible in user manuals or online. By changing these credentials to a strong and unique combination, you significantly reduce the risk of unauthorized access.
Another vital step is to regularly update your router’s firmware. Manufacturers frequently release updates that address vulnerabilities and improve security functionality. By ensuring your router is running the latest firmware, you close potential loopholes that cybercriminals could exploit. Most routers can be configured to check for firmware updates automatically, ensuring ongoing protection against the latest threats.
Disabling WPS (Wi-Fi Protected Setup) is also recommended as part of router hardening. While WPS can facilitate easier device connections, it poses security risks by allowing someone to gain network access through a PIN-based system that can be exploited. Disabling this feature helps fortify your network against unauthorized devices joining your home Wi-Fi.
Additionally, enabling WPA3 encryption is pivotal in securing your wireless network. This advanced security protocol offers strengthened defenses against eavesdropping and brute-force attacks. WPA3 encrypts the data transmitted over the network, making it significantly more challenging for unauthorized users to intercept or decipher the information being shared.
By diligently focusing on these steps—changing default login credentials, updating firmware, disabling WPS, and enabling WPA3—you can significantly enhance the security of your router and, consequently, your entire home network. Each action taken contributes to a reflexive assurance that your personal information and connected devices remain protected from potential threats.
Implementing Firewall Settings: Protecting Your Network
Firewalls serve as a vital component in safeguarding home networks, acting as a barrier between trusted internal networks and untrusted external networks. By monitoring and controlling incoming and outgoing traffic, firewalls help prevent unauthorized access and potential threats. Proper configuration of firewall settings on routers is essential for enhancing the security of your home network.
To begin with, accessing your router’s firewall settings typically involves logging into the router’s administrative interface. Each router model may have a different access point, often found through a web browser by entering the router’s IP address. Once logged in, navigate to the firewall settings section where you can initiate the configuration process. Users should ensure that the firewall is enabled, as this will initiate the protection protocols against unwanted traffic.
Creating specific rules within the firewall settings is another crucial step. These rules determine what types of traffic can be allowed or blocked. It is advisable to block all incoming traffic by default and then selectively allow traffic based on specific needs, such as for gaming or certain applications that require external access. Outgoing traffic should also be monitored and restricted to ensure that no unauthorized data leaves your network.
Understanding the significance of monitoring traffic is paramount. Users should periodically review the logs generated by the firewall, which can provide insights into any suspicious activity. This routine check is instrumental in identifying potential threats and responding promptly. Furthermore, many modern routers feature advanced firewall options, including intrusion detection systems and application layer filtering, which can provide an additional layer of security.
In essence, effectively implementing firewall settings is crucial for protecting your home network from unauthorized access and potential threats. With robust firewall rules and diligent traffic monitoring, individuals can significantly bolster their network’s security, creating a safer online environment.
The Importance of DNS Filtering: Enhancing Online Safety
Domain Name System (DNS) filtering has emerged as an essential method for improving online safety within home networks. DNS acts as the internet’s phonebook, translating human-friendly domain names into numerical IP addresses that computers use to communicate. However, a powerful feature of DNS is its ability to filter harmful content, significantly enhancing the security of connected devices.
By utilising DNS filtering, homeowners can effectively block access to malicious websites known for phishing schemes and malware distribution. When a user attempts to visit a site that is flagged as dangerous, the DNS service intervenes, preventing the connection to that website. This proactive measure can thwart numerous online threats, safeguarding personal information and reducing the risk of identity theft. Moreover, DNS filtering can bolster protection against unwanted content that might not be suitable for all household members, thus providing an additional layer of security for families.
Setting up DNS filtering is a straightforward process that can be accomplished through most home routers. Users can opt for reputable third-party DNS services, such as OpenDNS or Cloudflare, which offer built-in filtering capabilities. To initiate the process, access the router’s administrative backend, usually through a web browser. Here, users can input the DNS address provided by the chosen service. Additionally, many routers now come equipped with user-friendly interfaces that allow even less technically inclined individuals to implement these settings easily.
Once DNS filtering is integrated, network users can enjoy a safer online experience with reduced exposure to harmful sites. Furthermore, ongoing updates from DNS service providers ensure that the filtering remains effective against the latest online threats. Overall, employing DNS filtering is a practical and vital step towards enhancing online safety, providing individuals with peace of mind as they navigate the digital landscape.
Device Isolation: Segmenting IoT Devices
In the modern home, the proliferation of Internet of Things (IoT) devices has significantly transformed everyday living. However, with this convenience comes an increased risk of security vulnerabilities. Device isolation is a critical strategy that involves segmenting IoT devices from the main network traffic, thereby enhancing the security posture of a home network. By establishing separate sub-networks or virtual local area networks (VLANs) for these connected devices, homeowners can effectively contain potential security threats.
The primary benefit of isolating IoT devices is the reduction of the attack surface. Many IoT devices, from smart thermostats to security cameras, often operate with minimal security measures, making them attractive targets for attackers. By keeping these devices on a separate network, any potential intrusion is limited to the isolated segment, protecting the primary network used for more sensitive activities such as online banking or remote work. This segmentation also facilitates easier monitoring and management of these devices, as they can be tracked and analyzed without interfering with critical operations on the main network.
Implementing device isolation can be achieved through various methods. For instance, creating a guest network specifically for IoT devices is a straightforward approach. Additionally, some routers offer built-in features to create designated VLANs, allowing for advanced configurations that can further enhance security. It is advisable to regularly update the firmware of IoT devices and employ strong, unique passwords to bolster security within this isolated network. Furthermore, implementing network access control can restrict communication between devices on the isolated network, ensuring that only authorized devices may interact with one another.
In conclusion, the practice of isolating IoT devices is an essential measure that can significantly enhance home network security. By segmenting these devices, homeowners can mitigate risks, protect sensitive data, and maintain greater control over their connected appliances.
Best Practices for Managing Connected Devices
In the increasingly interconnected world, managing the devices connected to your home network is crucial for maintaining security and enhancing performance. One of the fundamental best practices is to ensure that all devices are regularly updated. Manufacturers frequently release firmware and software updates that address security vulnerabilities and improve functionality. By enabling automatic updates or setting aside time periodically to check for updates, users can protect their devices against the latest threats.
Monitoring device activity is another effective strategy in device management. Keeping track of which devices are connected to your network can help identify unauthorized access or unusual activity. A router’s administrative interface typically provides a list of all connected devices, allowing users to detect unfamiliar devices. Tools and applications are also available that can help monitor network traffic more thoroughly, giving insights into device usage patterns.
Furthermore, removing unused devices is essential for maintaining a secure network. Each connected device can serve as a potential entry point for cyberattacks, making it vital to disconnect devices that are no longer in use. This practice not only tightens network security but also contributes to better overall network performance by reducing congestion.
Implementing strong passwords for each device is also critical. Utilizing complex combinations of letters, numbers, and symbols increases resistance to brute-force attacks. Moreover, changing default passwords is necessary, as they are often easily accessible and known to potential attackers. Employing a password manager can assist in this endeavor, providing users with a secure way to generate and store unique passwords for each device.
By adhering to these best practices—regular updates, monitoring device activity, removing unused devices, and setting strong passwords—homeowners can create a more secure and efficient home network. This proactive approach significantly minimizes the risk of unauthorized access and enhances the overall integrity of your home network.
Monitoring Your Home Network: Tools and Techniques
Monitoring the security status of your home network is paramount in safeguarding sensitive information and ensuring that all connected devices function efficiently. Various tools and techniques are available to assist homeowners in tracking their network’s security posture effectively. One of the essential tools is a network scanner, which allows users to analyze devices connected to their network. These scanners can identify unauthorized devices attempting to access the network and assess the overall network health. Popular network scanning software includes Nmap and Angry IP Scanner, providing user-friendly interfaces and comprehensive information about connected devices.
In addition to network scanners, numerous security applications can bolster your home network’s security monitoring capabilities. These apps often provide real-time updates, alerts for suspicious activity, and advanced threat detection features. Programs like Fing and Avast’s Home Network Security offer insights into device statuses, potential vulnerabilities, and tips for improving network security. Utilizing such applications can help homeowners proactively address potential weaknesses in their security measures.
An often underutilized resource for monitoring is the logging feature available on most home routers. By enabling logging, homeowners can track network traffic patterns and identify anomalies that may indicate a security breach. This functionality is crucial for detecting unusual behavior, such as unexpected spikes in data usage or unfamiliar device connections. Regularly reviewing router logs can inform you about network performance trends and highlight any areas needing attention.
By leveraging these tools and techniques—network scanners, security apps, and router logging features—homeowners can maintain an effective monitoring system for their home networks. This proactive approach not only enhances the security and performance of the network but also establishes a culture of vigilance regarding home network management.
Conclusion: Ongoing Commitment to Network Security
Establishing a secure home network is crucial in today’s digital landscape, but it’s essential to recognize that this is not a one-time task. Cybersecurity is an ongoing process that requires continuous vigilance and adaptation. As technology evolves, so do the tactics employed by malicious actors. Threats can arise from various sources, including external attacks, outdated devices, and even human error. Therefore, maintaining the integrity and security of your home network must remain a priority.
To foster a robust cybersecurity posture, homeowners should stay informed about the latest developments in network security practices. This includes understanding newer threats and how to mitigate them effectively. Regularly reviewing the health of your network is also vital. This process involves checking configurations, ensuring that all devices are updated with the latest security patches, and monitoring network traffic for any suspicious activity. Utilizing advanced features like firewalls, DNS filtering, and device isolation can significantly enhance the security of your home network.
Moreover, fostering a culture of security awareness within the household is beneficial. Educating all users about safe browsing habits, recognizing phishing attempts, and understanding the importance of strong passwords can reduce the risk of breaches. Everyone in the household should contribute towards maintaining a secure environment. Consider scheduling regular audits of your home network to assess its security measures and identify areas in need of improvement.
In conclusion, an unwavering commitment to cybersecurity is essential for protecting your home network from the manifold threats present in the digital realm. By staying informed, conducting regular network evaluations, and fostering security awareness, you can ensure that your home remains a safe space in which to connect and thrive. Protecting your home network is a continuous journey, not merely a destination.